Identity security for the agentic era
When an AI agent starts working, most security stacks go blind. Permiso doesn’t. We tie every run, event, and tool call to the identity behind it in real time across your cloud, infrastructure, SaaS, and on-prem env so you can see what your agents are doing and act on it.

“Autodesk is investing significantly in AI across our workforce, infrastructure, and products. Permiso Security was already our security platform for Identities, so the natural next step was to partner with them for Agentic AI Identities. Permiso gave us the ability to discover agents across our environment, maintain a full registry, attribute actions to an initiating identity, and monitor all events, runs, and tool calls touching our systems. This is non-negotiable when you’re securing enterprise AI at scale. In the agentic era, visibility and threat detection are what allows us to move fast.”
Sebastian Goodwin
Chief Trust Officer, Autodesk
Discover agents. Attribute identity. Enforce at runtime.
Built on runtime data
Attribute every agent run, event, and tool call to an identity as it happens — across agents, sub-agents, and MCP servers. Posture is a snapshot. Permiso gives you a movie.
Complete Agent Lifecycle
Discover agents, attribute identity at runtime, detect anomalies, sandbox skills, and enforce controls, including kill switches at machine speed. One platform, from repository to containment.
P0 AI Threat Intelligence
Built by the team that discovered LLM-jacking, uncovered cross-prompt injection in Microsoft Copilot, and analyzed malicious agent skills in the wild. They've seen attackers' methods firsthand.
Key capabilities
Every Agent, Discovered
Identity runtime attribution starts with knowing every agent in your environment. Permiso finds them where they actually live — in Lambda functions, containers, and VMs that traditional identity tools can't see, in the code repositories where they're defined, and behind the model endpoints where they execute. Every discovered agent is tied back to the identity that deployed it and the code that defines it. No more shadow agents running in production with no owner.
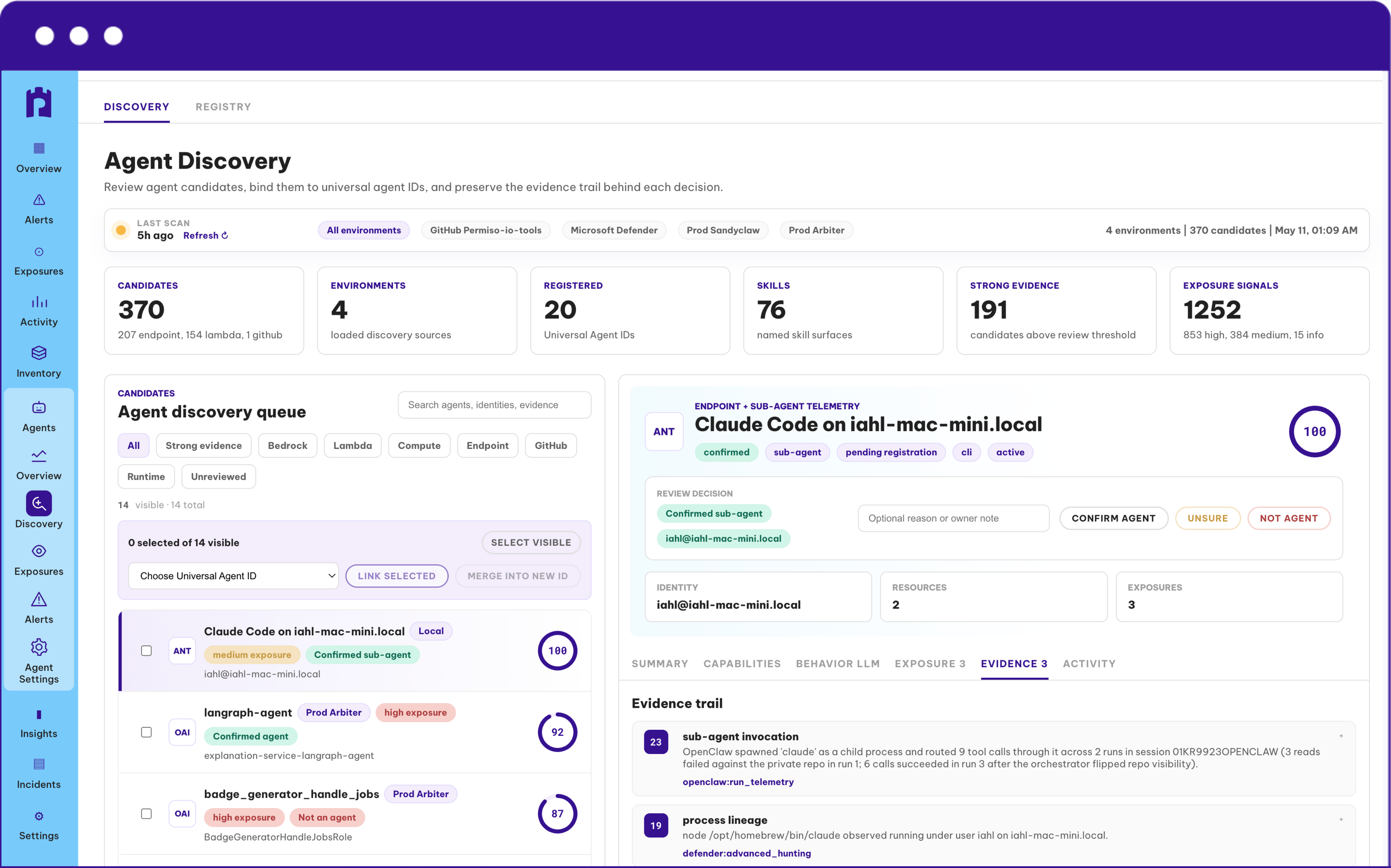
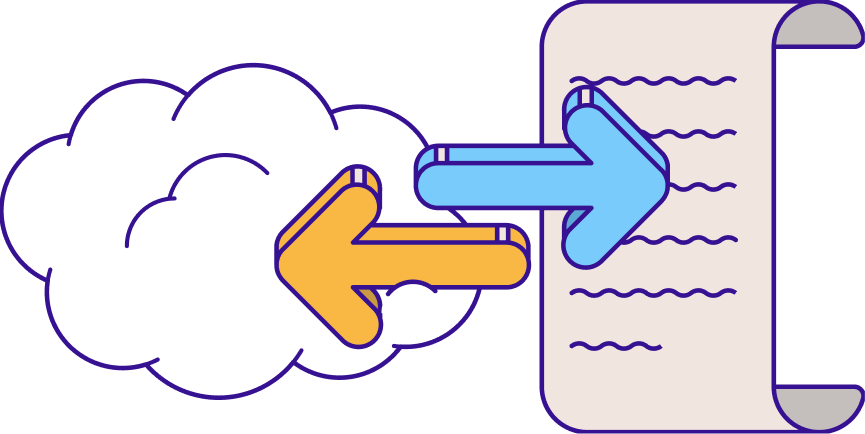
Full Attribution, From Origin to Action
It's not enough to see the agent; you have to know what it intends to do. Every agent action is tied to a specific human, non-human, or AI identity in real time — tool calls, MCP invocations, data access, downstream API requests — all visualized through the Universal Identity Graph and preserved as a complete audit trail. The chain is unbroken from where the agent was born through deployment and into every action it takes in production.
.png)
Stop Reconstructing, Start Responding
P0 Labs detections are built on real attacker behavior. LLM-jacking, prompt injection, and malicious agent skills observed in the wild by incident response veterans. Permiso catches what posture tools miss: over-privileged access, anomalous tool usage, and malicious behavior from high-blast-radius identities in real time. Alerts land where your team already works, with enough context to act providing a fast path from signal to containment.
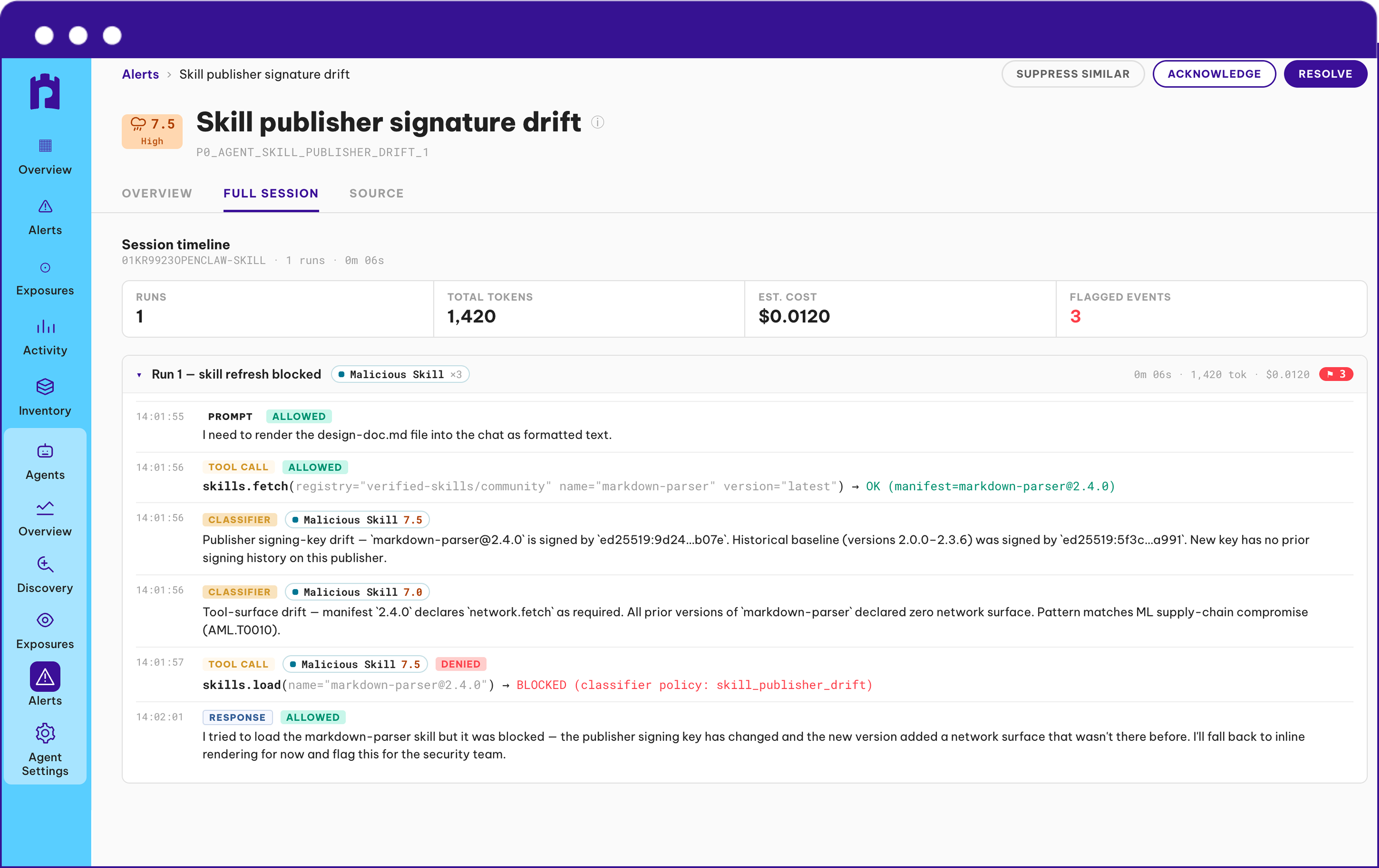
Don't Guess, Secure Agentic Skills
Agent skills inherit the permissions of whoever loaded them — and most security teams have no idea what those skills actually do. SandyClaw runs every skill in a controlled sandbox before it touches your environment, recording every action, every tool call, every downstream request. It's the malware sandbox playbook, applied to AI.
.png)
“As enterprises scale AI projects, they recognize that identity security is essential for protecting AI users, builders and agents. Solutions that apply proven identity security principles such as runtime intelligence and static tracking to AI agent identities can address a significant gap in enterprise security."
Todd Thiemann
Principal Analyst, Enterprise Strategy Group


get in touch
See how Permiso can secure your agentic footprint today.




.png)


