Detect Account Takeover
AUTHENTICATION BOUNDARIES ARE INSECURE
Due to the fragmented nature of identity security, most organizations are simply unaware that they have been compromised via an Account Takeover attack.

Why ATO Often Goes Undetected
As threat actors move from identity providers and into IaaS, SaaS, PaaS and CI/CD environments, the siloed nature of these systems makes detecting identity-based attacks nearly impossible.
How Permiso Detects Account Takeover
By creating a universal identity compromised of all of your human and non-human identities across all of your environments, Permiso can track wherever they go, what they do, and when they start to exhibit supspicious or malicious behavior. By creating a Universal Identity, Permiso is able to build sessions of activity to identity signs of account takeover.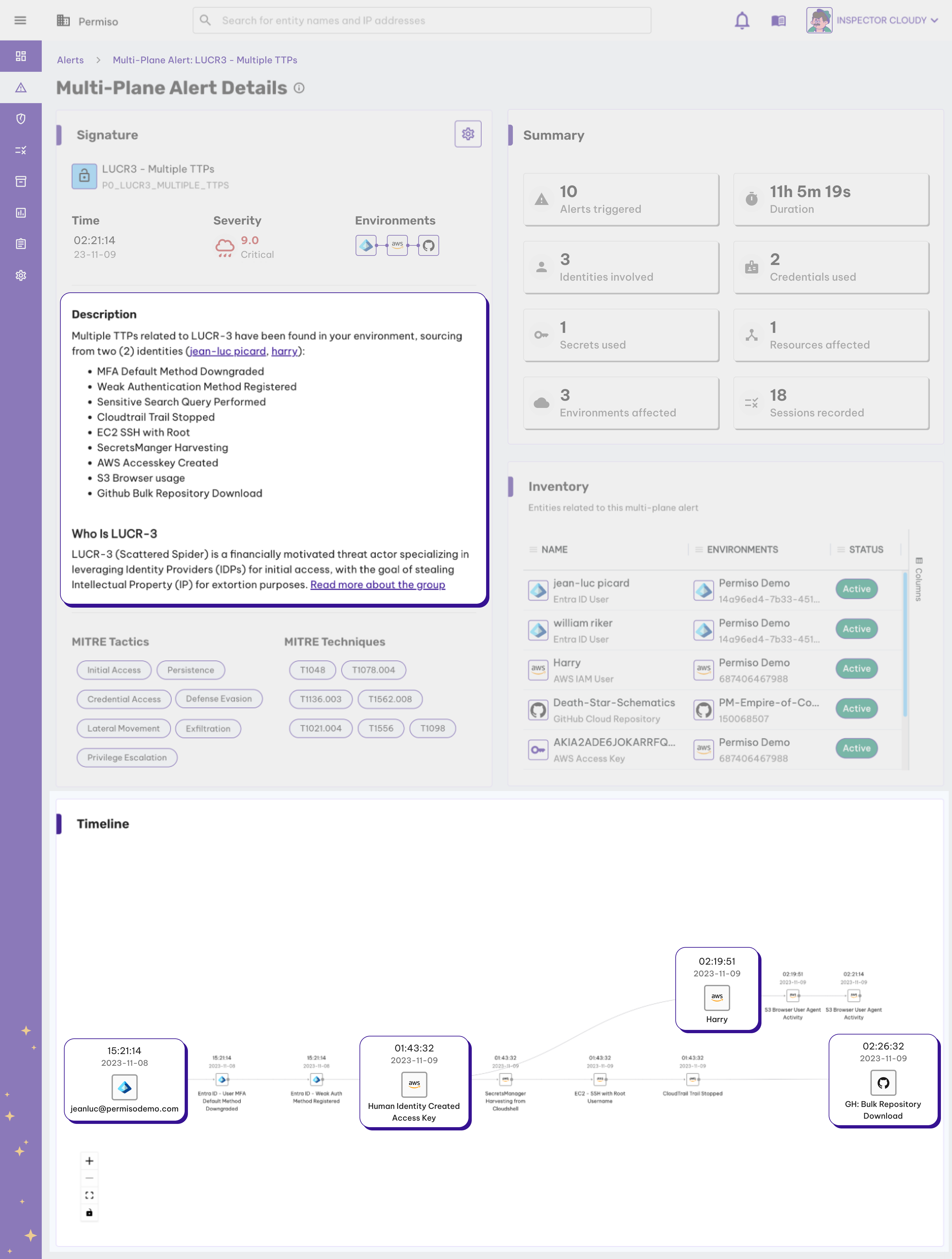
Why Traditional Tools Fail Against Modern Attacks
Security teams have attempted to leverage a combination of existing technologies like SIEM, CNAPP and CWP to try and solve the cloud threat detection problem. These tools weren't built to solve the modern attacks observed today where attackers hop between cloud environments and mask themselves with valid credentials.
Traditional tools have siloed focus (IaaS only), are event driven (noisy and high volume), and lack identity attribution context to expedite investigation time.
Want to see more?



.png)




