Permiso State of Identity Security 2024: A Shake-up in Identity Security Is Looming Large

Hear Ye, Hear Ye
Subscribe to Cloud Chronicles for the latest in cloud security!
Identity security is front, and center given all the recent breaches that include Microsoft, Okta, Cloudflare and Snowflake to name a few. Organizations are starting to realize that a shake-up is needed in terms of the way we approach identity security both from a strategic but also a technology vantage point.
Identity security is more than just provisioning access
The conventional view of viewing identity security as primarily concerned with provisioning and deprovisioning access for applications and services, often in a piecemeal manner, is no longer sufficient. This view was reflected as a broad theme in the Permiso Security State of Identity Security Report (2024), which finds that despite growing levels of confidence in the ability to identify security risk, nearly half of organizations (45%) remain “concerned” or “extremely concerned” about their current tools being able to detect and protect against identity security attacks.

The Permiso commissioned survey conducted over the summer, interviewed over 500 IT security and risk practitioners, with direct control or influence over security and risk decision-making. The findings reflect despite growing investment, maturity and confidence in cyber risk mitigation controls, organizations remain concerned in the face of advancing identity threats.
The key insights include:
- SaaS is seen as the riskiest environment.
- 93% of organizations stated that they can inventory identities across all environments, as well as track keys, tokens, certificates and any modifications that are made to any environment.
- 85% can determine “who is doing what” across fragmented authentication boundaries.
- 45% remain “concerned” or “extremely concerned” about their current tools being able to detect and protect against identity security attacks.
- 45% suffered an identity security incident in the last year, with impersonation attacks the leading threat vector.
Can you detect rogue identities?
Despite 86% of organizations stating that they can identify their riskiest identities (human and non-human), nearly half (45%) suffered an identity security incident in the last year, with impersonation attacks the leading threat vector -- revealing that social engineering-based attacks continue to be a pervasive threat to organizations.
When it came to the consequences for those that were breached, targeting sensitive data, which included personally identifiable information (PII) and intellectual property (IP), topped the list for 54% of those that were breached. 46% of organizations stated that the threat actors also escalated privileges and went after their supply chains (45%), both on the vendor and customer side.

Human identities remain a soft target
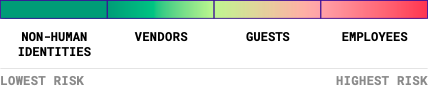
Another interesting finding was human identities are seen as the riskiest, with employees at the top of the list. Contrary to much of the market hype, non-human identities (API keys, OAuth tokens, service accounts) are seen as less risky than their human counterparts.
Identity security is siloed
It is not clear that organizations understand what identity security responsibility entails for the hybrid and multi cloud reality. Despite most organizations using on average 2.5 public clouds, the IT team (56%) was singled as being primarily responsible for ensuring the identity security for the organization across multiple environments. This may reflect identity still being seen as limited to access provisioning and deprovisioning. According to Jason Martin, Permiso Co-CEO and Co-Founder, this finding could be explained by “identity security traditionally having fallen under the general responsibilities for IT who are seen as stewards of IT systems, which includes provisioning access and securing identities. Only in a minority of organizations are we seeing the security department as the primary stakeholder for securing identities.”

Security budgets also appear to be siloed, with SaaS (87%) and IaaS (81%) environments getting the bulk of security spend vs all environments (46%). From a tooling perspective it appears that the IaaS layer (66%) has seen the bulk of the focus with a combination of cloud native security tools such as AWS GuardDuty and CNAPP solutions being used.
Although it appears that most organizations are “risk aware” to the cyber threats that they face, it is clear we have some way to go concerning having the ability to detect and respond to identity threats as they arise. In fact, being able to detect and prevent credential compromise, account takeover and insider threat was cited as the leading concern for organizations.
Towards universal identity security
It's up to all of us, the vendors, organizations and the broader security community to reimagine what is needed from a people, process and technology standpoint to secure the new reality of human and non-human identity as the leading threat vector. In this regard we need to recast identity security from merely provisioning or de-provisioning access to applications and services, to viewing it as a strategic business enabler.
Permiso Security was born to address this challenge, making unified identity security for all identities, across all environments, a reality.
You can access the full report here: https://hero.permiso.io/state-of-identity-security-survey-report-2024
Interested in learning more? Reach out for a demo.



.png)





-1.png?width=767&name=image%20(7)-1.png)

.png?width=767&name=image%20(9).png)
