
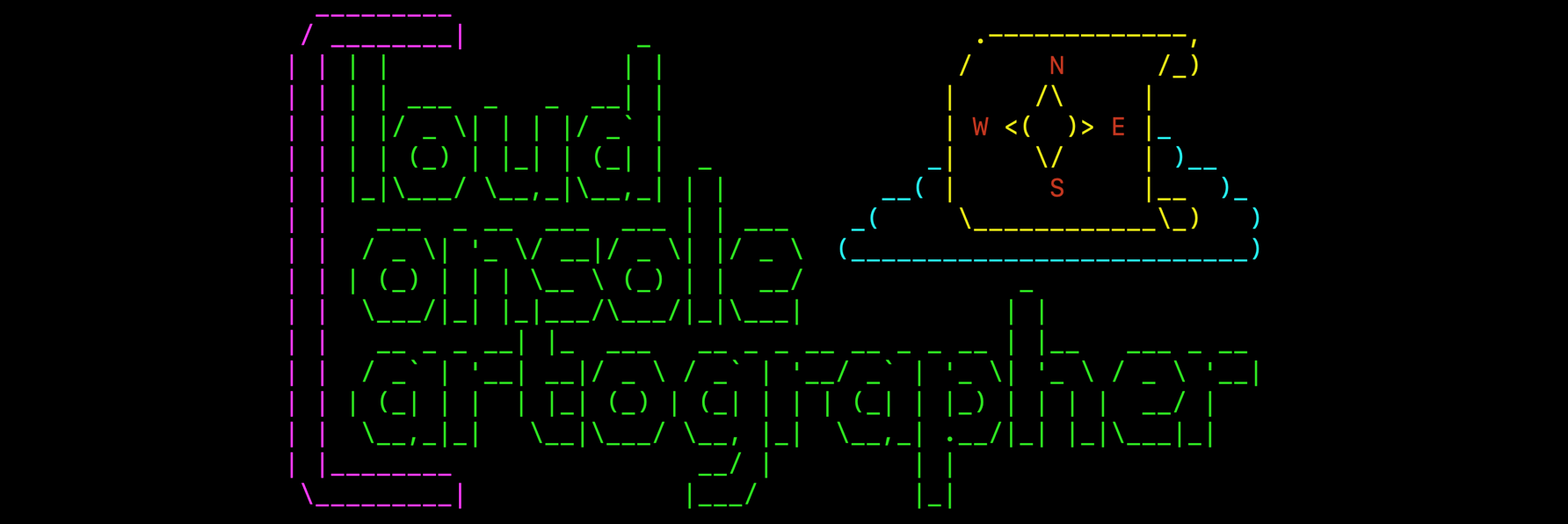
Permiso Launches Cloud Console Cartographer to Help Security Teams Make Sense of Console Activity in Cloud Logs
Hear Ye, Hear Ye
Subscribe to Cloud Chronicles for the latest in cloud security!
The open-source tool helps security teams easily transcribe log activity generated from events of AWS console sessions
PALO ALTO, CA – April 18, 2024 – On the heels of announcing their Series A fundraising and releasing an open-source cloud threat detection tool, CloudGrappler, Permiso has announced the launch of Cloud Console Cartographer, an open-source tool that helps security teams make sense of console-driven event activity in their AWS logs. The tool, which maps noisy log activity into highly consolidated, succinct events, helps security practitioners quickly cut through the noise to better understand console behavior in their environment.
When a user accesses the AWS console and clicks on IAM → Users, that single action creates 300+ CloudTrail events. The console events that are showing in CloudTrail are API calls that ultimately populate what is being displayed within the user interface. A console session, therefore, can have far more events than the actual inputs, or actions (such as clicking on an IAM homepage) and these events are never explicitly associated with the user’s actions.
“Permiso and the P0 Labs research team continue to leverage their threat hunting experience by developing tools that help defenders understand and secure their cloud environments,” said Will Bengtson, Senior Director of Security Engineering at Hashicorp. “Cloud Console Cartographer helps security teams triage threats more quickly by aggregating log data from AWS console activity and mapping it back to the originating input actions by the user in the UI. This helps security teams cut through the noise and quickly differentiate between intended actions and unintended attacks. Their research and open-source tooling demonstrates the experience they have with helping organizations detect and respond to threats in the cloud.”
In reviewing these logs, you might see events in CloudTrail such as iam:ListMFADevices or iam:ListAccessKeys. This can be confusing, because this user didn’t take any action in the UI to list MFA devices or Access Keys; this user simply clicked on the IAM homepage which triggered these events to populate that information in the console UI. Security professionals are left trying to differentiate API calls specifically invoked by a user from those secondary API invocations that create events to support the behavior or actions being conducted in the console UI. Threat actors have been observed leveraging console and other UIs in a strategic effort knowing how confusing this log data can be to incident responders and blue teamers.
“If you’ve spent any amount of time digging through logs trying to triage activity in an environment, you’ve probably been overwhelmed with the log data that comes from console activity,” explained Permiso’s Principal Threat Researcher, Daniel Bohannon. “Threat actors are aware of how confusing parsing this data can be and will often leverage GUI tools in order to better cover their tracks or deceive defenders who are tracking them in an environment.”
Cloud Console Cartographer processes raw events in a log and is able to determine and group a series of 17 events that they are seeing in CloudTrail is someone clicking a particular button in the UI. Cloud Console Cartographer even parses additional data from these secondary events to provide more context about what the user was seeing in the console, like the names of the groups, policies, roles or access keys that were active at the time the click occurred. The ability to correlate and reduce these events into singular actions helps security teams gain a quick understanding of what activity was conducted in console, something that is difficult to do today.
“If you click on IAM users in console, and there are three users listed, that generates 18 events in CloudTrail,” Bohannon explained. “If you have 20 users being listed, that will generate 141 events. This number incrementally grows where listing 100 users generates 701 events in CloudTrail - all from a single click of a button in the user interface.”
About Permiso
Permiso is an identity threat detection company that finds evil in cloud-based environments. Permiso creates session constructs for the identities across cloud and SaaS applications to break down visibility boundaries and understand user behavior and intent across your environment. These session constructs are developed by stitching together activity across cloud applications, services, and providers to create an immutable ledger of activity in an environment. Permiso creates a unified identity across authentication boundaries and presents this as a forensically sound access chain. By tying all activity back to a singular identity, Permiso is able to detect access anomalies, behavioral anomalies, or specific activities associated with compromised credentials. For more information, please visit our website or find us on Twitter and LinkedIn.



.png)





%20(2).png?width=767&name=Blog%20Image%20(892%20x%20298)%20(2).png)
.png?width=767&name=(970x250).png)
