Vendors Shouldn't Be Breached
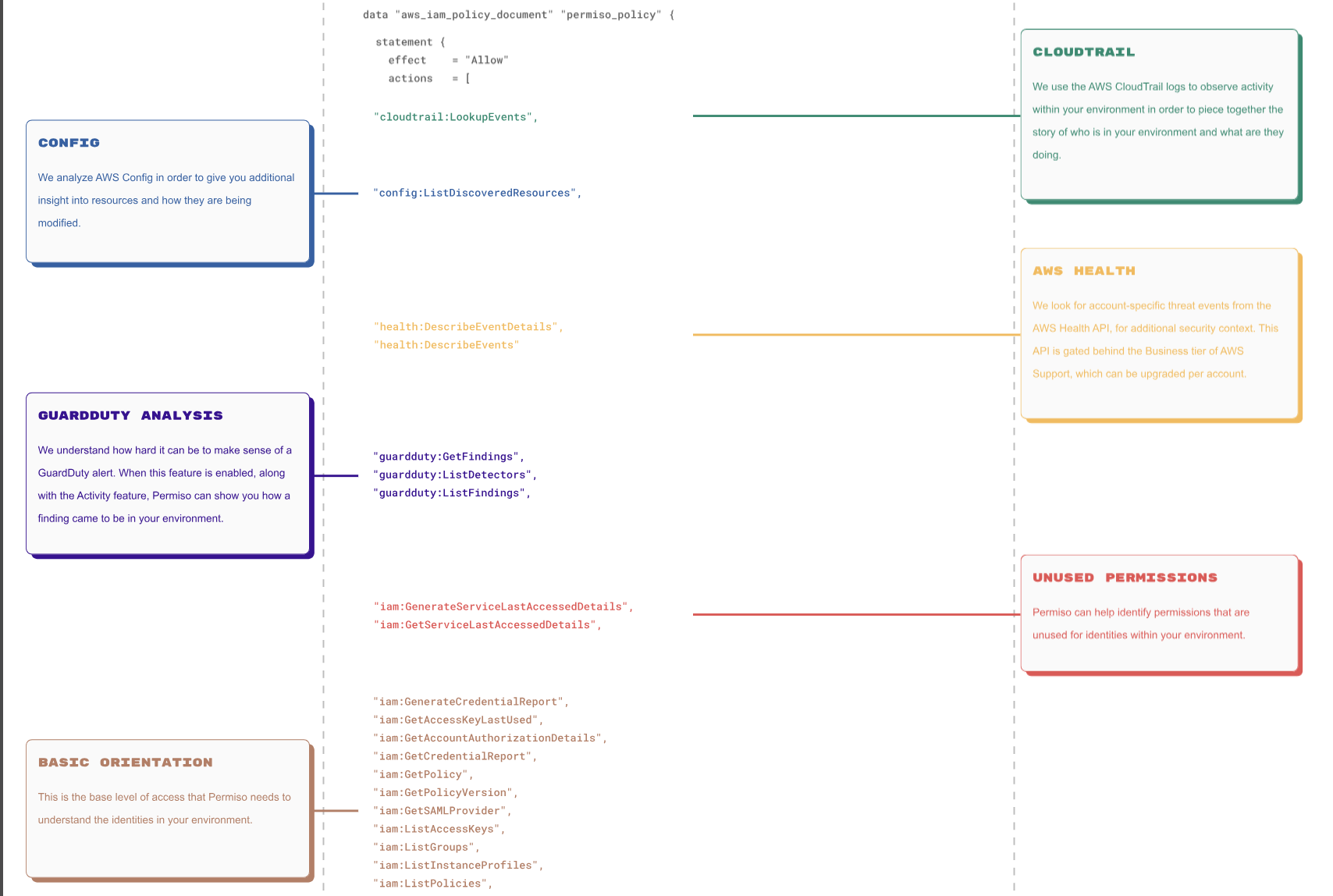
Permiso is read only and unlike many other cloud vendors, only request privileges we need. We only monitor your control plane and aren't exposed to any underlying or transaction data.
Introducing Cloud Console Cartographer: An Open-Source Tool To Help Security Teams Easily Understand Log Events Generated by AWS Console Activity
Daniel Bohannon | 04.18.24
We Encrypt All Data
In Transit and At Rest
The data that we do maintain, control plane data, is encrypted at rest, as well as in transit.

We Dog Food Our Own Stuff
All identities are federated in the Permiso product. Local users and vendors are continuously monitored in our environment.

Our Sub-processors
Brands we use to build Permiso's platform.

Monitored by P0 Experts Using Permiso

Daniel Bohannon
Principal Threat Researcher
UGA B.S. CompSci, Georgia Tech M.S. InfoSec, 13+ years IR & researcher roles including Mandiant Advanced Practices Team & Microsoft, OpenSource tool developer (e.g. Invoke-Obfuscation)
My favorite dessert is a lavender latte - to be enjoyed during or between any meal of the day
Andrew Kraut
Senior Threat Researcher
Born with a screwdriver in his hand, Andy has been digging into the internals of technology since he opened his eyes and in the security industry since the era of dial-up. Proudly a generalist, Andy has turned his hand at a wide swath of security industry focuses on both the offensive and defensive sides over the last 25 years. When he’s not breaking systems and questioning assumptions, you can find him suspiciously connecting his laptop to things, pushing buttons that say “Do not press,” biking mountains, and climbing rocks.
My favorite dessert is chocolate marshmallow churro fries (from Award Weiners at Disney’s California Adventure).


Ricardo Arancibia
Data Scientist
~4 years of experience solving problems using Data Science and building end-to-end ML solutions in a wide variety of industries. Co-founded an official ML Google community with +500 members.
My favorite dessert is any and all combinations of coffee and chocolate. I enjoy coffee in my chocolate and chocolate in my coffee.
Andi Ahmeti
Associate Threat Researcher
Experienced Computer Engineering senior student with a 6-month internship as a Security Engineer. Passionate about cybersecurity and skilled in software development, hardware design, and system architecture.
My favorite dessert is any and all combinations of coffee and chocolate. I enjoy coffee in my chocolate and chocolate in my coffee.
Abian Morina
Associate Threat Researcher
Computer Science and Engineering student specializing in Information Security and Assurance. 1+ year of experience as a Penetration Tester/Bounty Hunter.
My favorite dessert is any and all combinations of coffee and chocolate. I enjoy coffee in my chocolate and chocolate in my coffee.
Enisa Hoxhaxhiku
Associate Threat Researcher
Highly motivated and proactive Computer Science and Engineering student deeply passionate about Information Security and Cybersecurity. Interned in Information Security, actively engaging in red team and blue team activities. Possesses a strong analytical mindset and attention to detail.
My favorite dessert is any and all combinations of coffee and chocolate. I enjoy coffee in my chocolate and chocolate in my coffee.
Art Ukshini
Associate Threat Researcher
Experienced Cyber Security Engineer with a background in Computer Engineering studies. Highly passionate on Offensive Security & with a strategic approach on Defensive Security & Threat Research.
My favorite dessert is any and all combinations of coffee and chocolate. I enjoy coffee in my chocolate and chocolate in my coffee.
Dredhza Braina
Associate Threat Researcher
Computer engineering graduate with experience as a Software Engineer and DevSecOps Engineer/SRE. Focused on threat research and deeply dedicated to cybersecurity.
My favorite dessert is any and all combinations of coffee and chocolate. I enjoy coffee in my chocolate and chocolate in my coffee.

Ela Dogjani
Threat Research Intern
Senior Software Engineering student at Canadian Institute of Technology, Albania. Began tech journey at 14 with STEM trainings. Now exploring security, excited for Permiso internship.
My favorite dessert is any and all combinations of coffee and chocolate. I enjoy coffee in my chocolate and chocolate in my coffee.


