Attackers Have The Creds To Your Kingdom
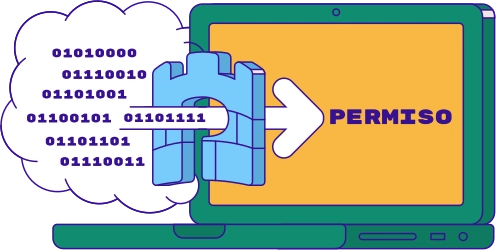
Attackers are plundering across IaaS, SaaS, CI/CD, and IDP environments, as we saw with LUCR-3 (Scattered Spider). Using shared credentials, attackers can cover their tracks, leaving it hard to know which identity did what. Permiso traces them every step of the way, connects sessions, and exposes suspicious and malicious behavior.



.png)